More than 11 million phishing links blocked in 1 year, Vietnam is at the top-Information Technology
Remote working has created many opportunities for hackers to deceive companies’ information over the past two years.
Cybercriminals are constantly coming up with new methods to send spam and phishing messages to both individuals and businesses. Armed with knowledge of the latest trends, they leverage the dizzying shift in digital habits during the COVID-19 pandemic to launch non-technical attacks like phishing emails.
Kaspersky data shows that, by including hot topics and phrases related to users’ online activities (such as shopping, entertainment streaming, COVID-19 pandemic,…) in the news. message, the chances of an unsuspecting user clicking on an infected link or malicious attachment are greatly increased.
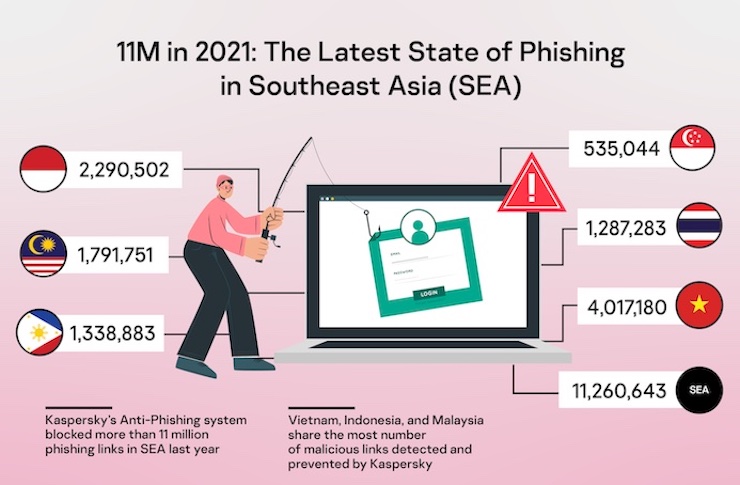
In 2021 alone, Kaspersky’s Anti-Phishing system blocked a total of 11,260,643 phishing links in Southeast Asia. Most of them were blocked on the devices of Kaspersky users in Vietnam, Indonesia and Malaysia.
“Email remains our main method of communication at work in Southeast Asia, and 11 million phishing attempts a year are just the tip of the iceberg. With all the important data sent via email, cybercriminals can see it as an efficient and lucrative entry point. An unfortunate example is the $81 million Bangladesh bank heist in 2016, which was successfully accomplished by a targeted phishing attack,” said Yeo Siang Tiong, Southeast Regional General Manager. Kaspersky’s Asia said.
Globally, 253,365,212 phishing links were detected and knocked down by Kaspersky solutions last year. In total, 8.20% of Kaspersky users in different countries and regions around the world have faced at least one phishing attack.
Kaspersky added that remote working has created many opportunities for hackers to deceive companies’ information over the past two years. One of the increasing trends is business e-mail fraud (Business e-mail compromise – BEC). BEC attacks are a type of phishing that involves impersonating a representative from a trusted business.
According to Verizon, this is the second most common type of non-technical attack in 2021, and the FBI reported that BEC attacks cost US businesses more than $2 billion between 2014 and 2019.
Kaspersky experts are witnessing more and more BEC attacks. During the fourth quarter of 2021, Kaspersky products prevented more than 8,000 BEC attacks, with the largest number (5,037) occurring in October.
Throughout 2021, the company’s researchers closely analyzed how scammers create and distribute fake emails. As a result, they found that attacks tended to fall into two categories: large-scale and highly targeted.
This method was formerly known as “BEC-as-a-Service”. Accordingly, the attacks simplify the mechanism behind the attack to reach as many victims as possible. The attackers sent mass streamlined messages from free mail accounts, hoping to entice as many victims as possible. Such messages often lack a high degree of sophistication, but they are effective.
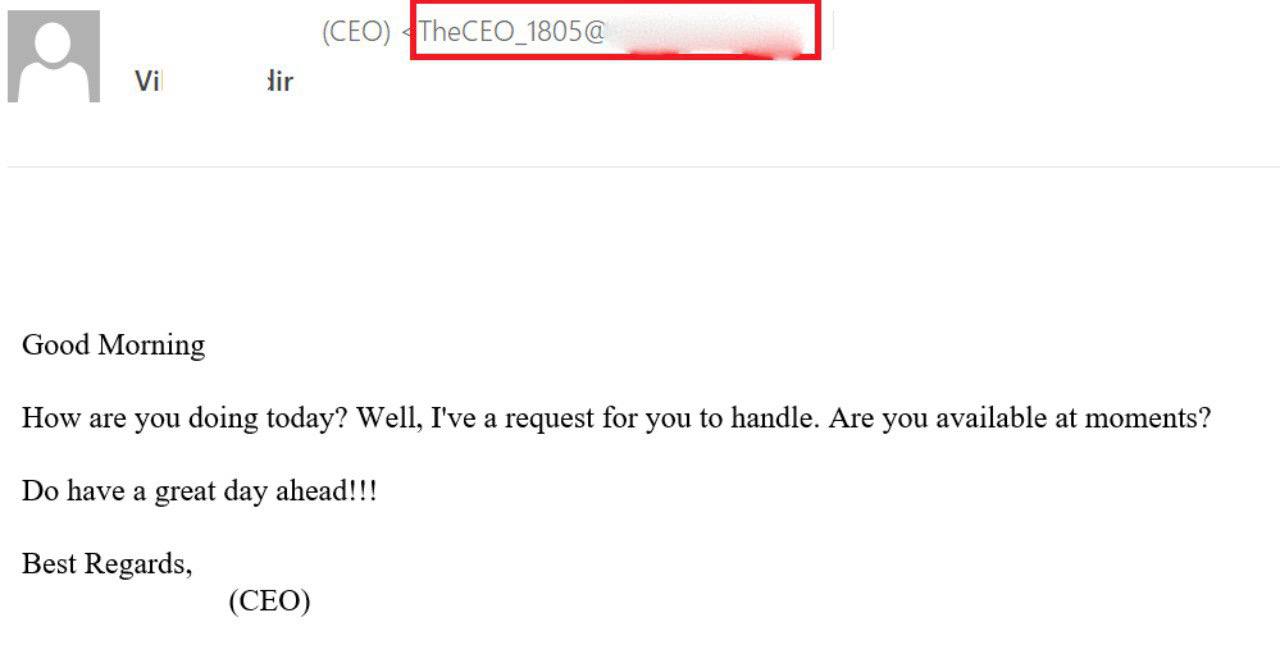
An example of a large-scale CEO fraud campaign.
In this case, an employee received a fake email from a higher-level colleague. The message is always vaguely indicating a person has a processing request. Victims may be asked to make quick payments on certain contracts, resolve some financial conflicts, or share sensitive information with third parties. Any employee can become a victim. Of course, there are some notable warning signs in such a message.
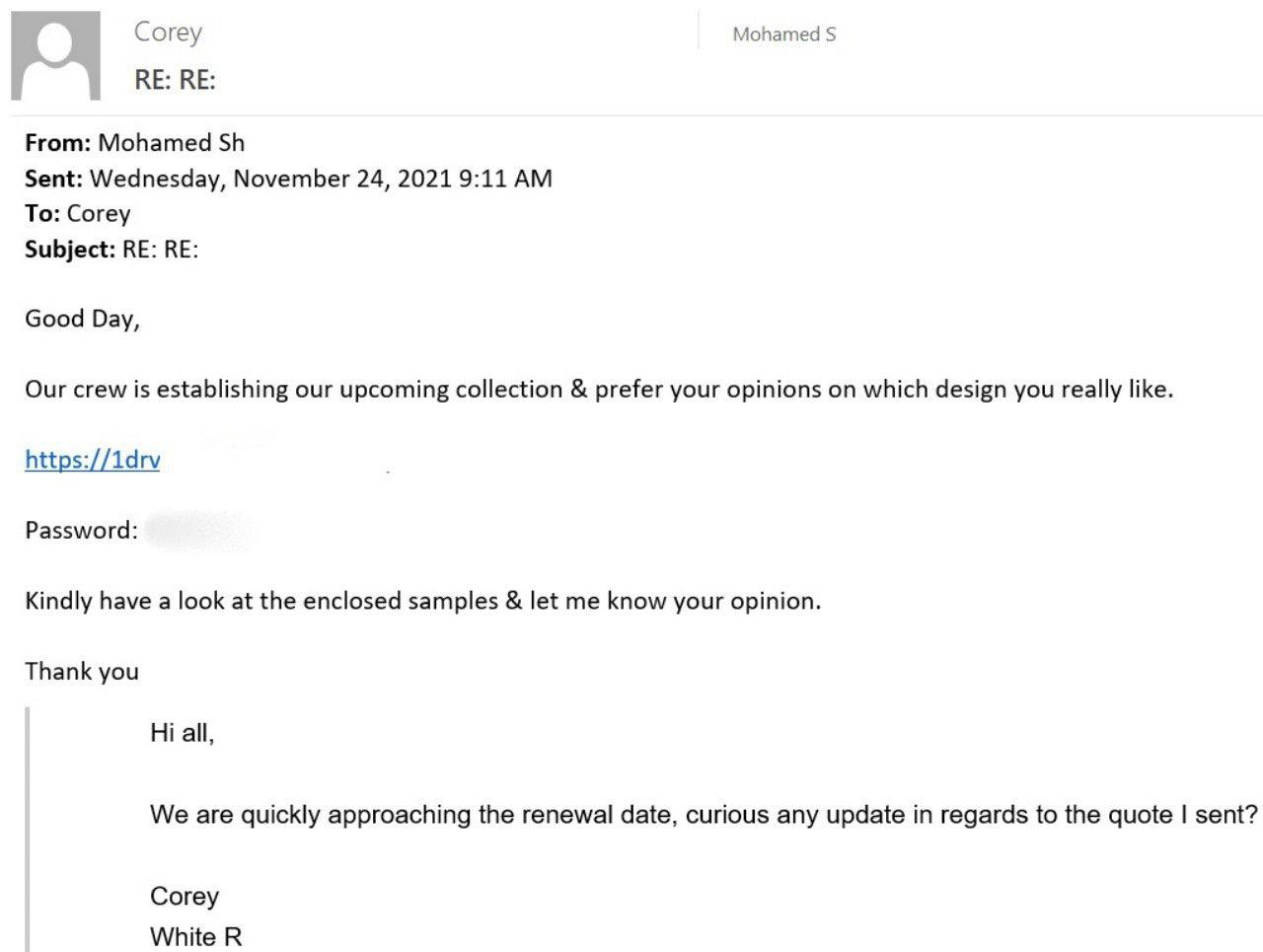
At the same time, some criminals are relying on simplified mass mailing, others are moving towards more advanced targeted BEC attacks. The process works like this: Attackers first attack a man-in-the-middle mailbox, gaining access to that account’s e-mail. Then, when they find matching messages in the compromised mailbox of the intermediary, they resume correspondence with the targeted company, impersonating the intermediary. Often the aim is to convince the victim to transfer money or install malware.
In fact, the goal is to join the conversation mentioned by the attackers, they are more likely to fall victim to the scam. Such attacks have proven to be highly effective and that is why they are not only used by small-scale criminals looking to make a quick profit.
According to Ngoc Pham (Vietnamese people)
at Blogtuan.info – Source: 24h.com.vn – Read the original article here