A “familiar” app that is suspected of stealing money from a bank account, remove it immediately!
Tom’s Guide Reportedly, in a recent discovery, Android device users have become the target of dangerous malicious code with the ability to steal data, bank accounts and take control of the victim’s phone.
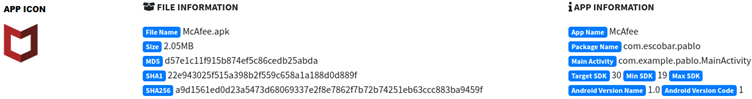
Dubbed “Escobar”, this dangerous trojan targets customers from 190 financial institutions across 18 countries. By masquerading as McAfee anti-virus application, this application has successfully tricked many Android users into downloading it to their devices.
The fake McAfee application contains dangerous trojans capable of taking control of the victim’s device (Image: Cyble)
Malicious App Insights
According to the security experts of Cyblethis case once again shows why users should be careful when installing apps from 3rd party app stores onto their devices.
The findings show that, when the user Android Installing the fake McAfee application on the device, the malicious code “Escobar” installed in the application will perform a series of dangerous tasks such as:luster steal SMS text messages and multimedia files, make phone calls, track victim’s location, use phone’s camera, uninstall apps, insert new URLs into web browsers, and the most dangerous is to take control of the device remotely.
This allows the development team application can break into your online banking account and other online services like email, social media accounts without any permission from you.
What to do to prevent the attack of trojan Escobar?
According to advice from security experts, users should be vigilant and not download any applications from any third-party sources.
This is the best way you can protect yourself from Escobar malware. In addition, you also note the following to prevent the attack of dangerous trojans.

Users should be vigilant and not download any apps from any third-party sources (Image: Getty)
- 1. Enable the Google Play Protect option on your Android phone, which will warn if the user installs malware on their device.
- 2. Every time you install an application, you should carefully read the application’s system access permission request. Remove unnecessary requests and do not install apps when suspicious permission requests are detected.
- 3. Always check the details like name, description, app developer and reviews,… before installing the app on the device.
4. Avoid installing apps from outside the Google Play Store.
5. Install a trusted antivirus app and scan your device.
at Blogtuan.info – Source: Kenh14.Vn – Read the original article here



